The zero-trust governance layer
for AI agents.
Docker isolates environments. Envpod governs access to real ones.
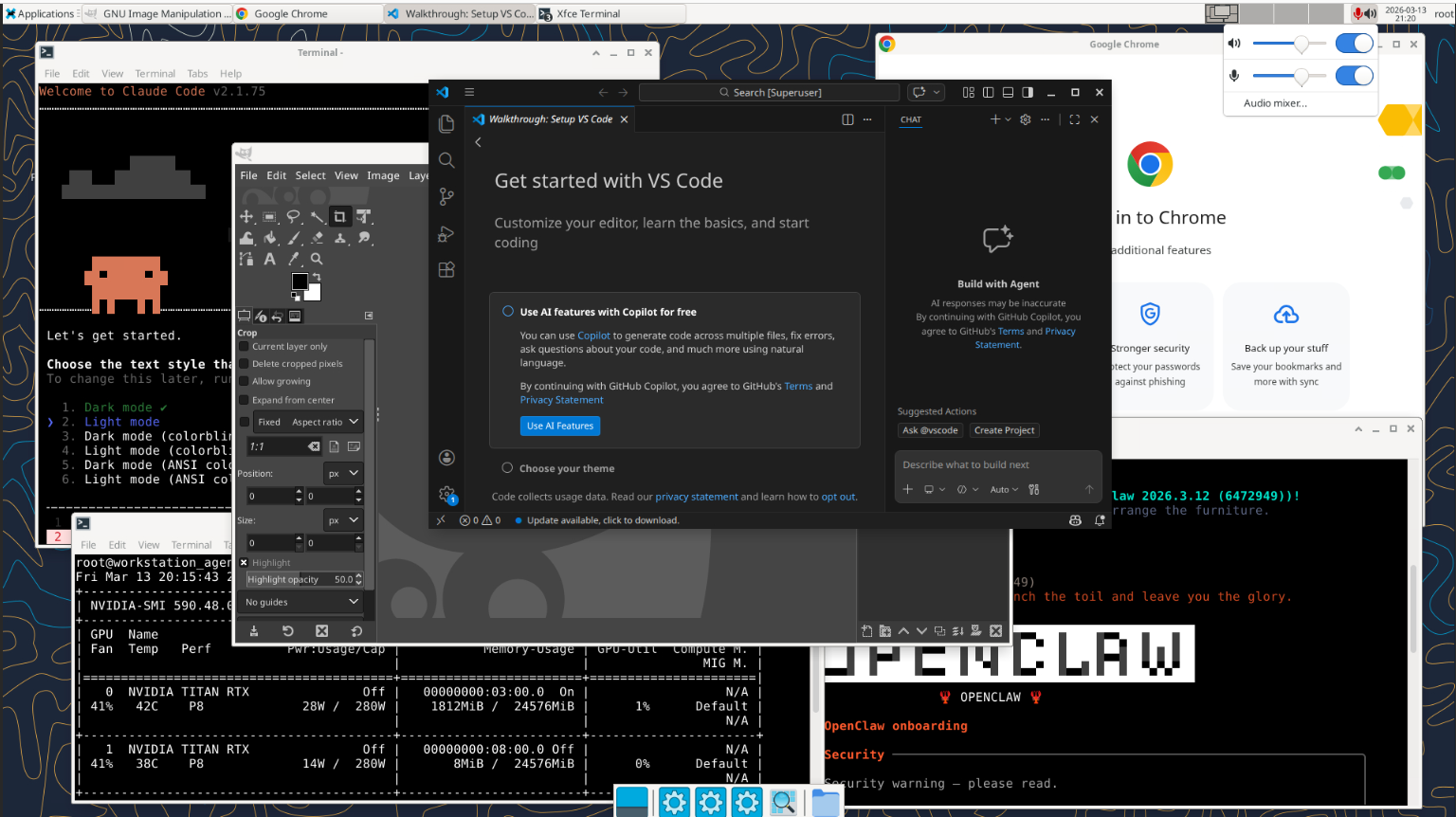
AI agents are only useful when they can work with your real files, tools, and workflows. But direct host access breaks the trust model. Envpod lets agents work in your real environment through a copy-on-write layer, so every change is reviewable before it reaches the host.